Welcome to the world of cybersecurity, where PHP takes center stage as a powerful ally in safeguarding digital assets across platforms. In this blog post, we delve into the realm of PHP and its pivotal role in fortifying cyber defenses with cross-platform solutions. Join us on this journey through the intricacies of PHP and discover how it enhances security measures for organizations worldwide. Let’s explore the dynamic intersection of PHP and cybersecurity together!
What is PHP?
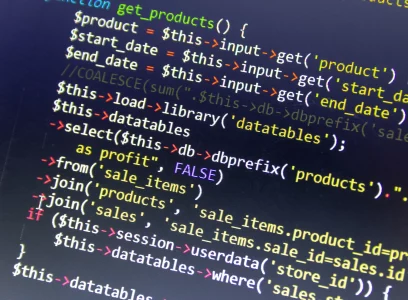
PHP, which stands for Hypertext Preprocessor, is a versatile scripting language commonly used for web development. It seamlessly integrates with HTML to create dynamic and interactive web pages. PHP code is executed on the server-side, generating content that is then sent to the client’s browser. This open-source language supports various databases like MySQL, making it a popular choice for building robust web applications.
One of PHP’s strengths lies in its flexibility and ease of use, allowing developers to quickly prototype and deploy solutions. With a vast community contributing plugins and libraries, PHP offers extensive functionality out of the box. Its syntax resembles C programming languages, making it accessible to programmers familiar with similar structures.
PHP empowers developers to craft responsive websites and applications efficiently while maintaining security standards essential in today’s digital landscape.
The Role of PHP in Cybersecurity
PHP plays a crucial role in cybersecurity by providing developers with a powerful and versatile scripting language to build secure web applications. Its ability to handle encryption, authentication, and data validation makes it an essential tool for implementing robust security measures.
With PHP’s built-in functions and libraries, developers can easily integrate security features such as input filtering, access control, and secure communication protocols into their applications. This helps in safeguarding sensitive information from unauthorized access or malicious attacks.
PHP’s open-source nature allows the community to constantly improve its security features through updates and patches. This collaborative effort ensures that PHP remains a reliable choice for developing secure solutions in an ever-evolving cyber threat landscape.
PHP serves as a foundation for building resilient cybersecurity solutions that protect against vulnerabilities and enhance overall system defenses. Its flexibility and scalability make it an ideal choice for businesses looking to fortify their digital assets against potential threats.
Cross-Platform Compatibility of PHP
When it comes to cybersecurity solutions, the ability to seamlessly work across different platforms is crucial. PHP, a versatile scripting language, excels in this aspect by offering excellent cross-platform compatibility. Whether you’re using Windows, macOS, or Linux systems, PHP can be easily integrated and deployed without any hassle.
This flexibility allows cybersecurity professionals to develop robust applications that can run smoothly on various operating systems. With PHP’s cross-platform capabilities, organizations can ensure consistent protection against cyber threats across all devices and platforms they operate on.
The ease of transitioning between different environments due to PHP’s compatibility simplifies the development process and reduces potential errors or vulnerabilities that may arise from platform inconsistencies. This makes PHP an ideal choice for creating secure and reliable cybersecurity solutions that cater to diverse technological landscapes.
PHP’s cross-platform compatibility opens up a world of possibilities for implementing effective cybersecurity measures regardless of the operating system environment being used.
Advantages of Using PHP for Cybersecurity Solutions
When it comes to cybersecurity solutions, PHP offers a range of advantages that make it a popular choice among developers and security professionals alike. One key advantage is its versatility – PHP can be used for various security applications such as web application firewalls, intrusion detection systems, and secure data encryption.
Another benefit of using PHP for cybersecurity is its cross-platform compatibility. This means that PHP-based security tools can run on different operating systems without requiring extensive modifications or additional resources. This makes it easier for organizations with diverse IT environments to implement robust security measures effectively.
PHP’s open-source nature allows developers to access a wealth of community-driven resources and libraries dedicated to cybersecurity. This not only speeds up the development process but also ensures that the latest security updates and best practices are readily available.
PHP’s scalability enables organizations to customize their cybersecurity solutions according to their specific requirements and scale them as needed without compromising performance or reliability.
Successful Implementation of PHP in Cybersecurity
In the realm of cybersecurity, PHP has proven its versatility and effectiveness in safeguarding critical systems. Several case studies illustrate successful implementations of PHP in enhancing security measures across various platforms. One notable example is a leading e-commerce website that utilized PHP to strengthen its defenses against cyber threats, resulting in a significant reduction in vulnerabilities and attacks.
Another case study involves a financial institution that integrated PHP into their security protocols to secure customer data and prevent unauthorized access. By leveraging the flexibility of PHP, they were able to fortify their systems and uphold regulatory compliance standards effectively.
Healthcare organization implemented PHP-based solutions to protect sensitive patient information from breaches and ensure HIPAA compliance. The seamless integration of PHP bolstered their cybersecurity framework, mitigating risks associated with data breaches and ensuring patient confidentiality.
These success stories highlight the adaptability and reliability of PHP as a cross-platform cybersecurity solution that can be tailored to meet diverse industry needs effectively.
Challenges and Limitations of PHP in Cybersecurity
While PHP offers many advantages in cybersecurity, it also comes with its own set of challenges and limitations. One common issue is the need for regular updates to address security vulnerabilities that may arise. This constant maintenance can be time-consuming and require a dedicated effort from developers.
Another challenge is ensuring proper validation of user input to prevent malicious attacks like SQL injection or cross-site scripting. Without thorough validation, sensitive data could be compromised, leading to potential security breaches.
PHP’s open-source nature means that code libraries and plugins may not always undergo rigorous security testing before being integrated into projects. This poses a risk as vulnerabilities in third-party components could expose systems to cyber threats.
PHP’s flexibility can sometimes lead to coding errors or misconfigurations that inadvertently weaken the overall security posture of an application. It requires skilled developers who are well-versed in best practices for secure coding to mitigate these risks effectively.
Conclusion
PHP is a powerful and versatile tool in the realm of cybersecurity. With its cross-platform compatibility, it offers a flexible solution for protecting systems across different operating environments. The advantages of using PHP for cybersecurity solutions are evident through successful case studies that showcase its effectiveness in safeguarding against cyber threats.
While PHP has its challenges and limitations, such as potential vulnerabilities if not properly managed or outdated code being exploited by attackers, it remains a valuable asset for organizations looking to enhance their security measures.
PHP continues to play a vital role in strengthening cybersecurity defenses and is likely to remain an essential component in the fight against evolving cyber threats. Organizations can leverage the capabilities of PHP to bolster their security posture and protect sensitive data from malicious actors on various platforms.